Honeywell Process Solutions (HPS) opened its Industrial Cyber Security Lab to advance its development and testing of technologies and software to defend industrial facilities and operations, such as refineries and manufacturing plants, against cyber attacks.
The grand opening of Honeywell Process Solutions’ (HPS) Industrial Cyber Security Lab in Duluth, Ga., featured Jeff Zindel, global cyber security business leader; Mike Spear, global operations manager; and Eric Knapp, director of cyber security solutions and technology. The trio took turns describing the lab and its functions and the types of cyber security vulnerabilities the lab was designed to protect against. The lab includes a model of a complete process control network that Honeywell cyber security personnel will use for research and hands-on training, and to develop, test, and certify industrial cyber security protection. The lab’s speciality is process control combined with cyber security.
Knapp said that cyber security attacks boil down to only two types: insider-accidental and outsider-intentional attacks. An insider breach is generally an accident caused by one of the employees working at a facility. It can be as simple as clicking on a phishing link in an email or uploading a file from a corrupted flash drive or portable media device.
In many cases, plants and other facilities are running legacy software such as Microsoft Windows XP, which is no longer supported by Microsoft and therefore does not receive software updates or security patches. The lab is designed to protect against these attacks by assuming a role of active defense, looking for suspicious activity on the network and putting a stop to it immediately.
Becoming an active defender
The cyber security lab offers full protection, system integration, cyber security, and management of said solutions. The goal of this lab is to make companies take a hard stance against cyber attacks by integrating offerings and making organizations dynamic and active defenders. To become an active defender, companies must be aware of the cyber threat and must also make their employees aware of this threat. Vigilance and awareness of cyber security threats should be absorbed into company culture so that it becomes second nature, like remembering to wear a hardhat on the plant floor.
Gauging the risk and setting a baseline
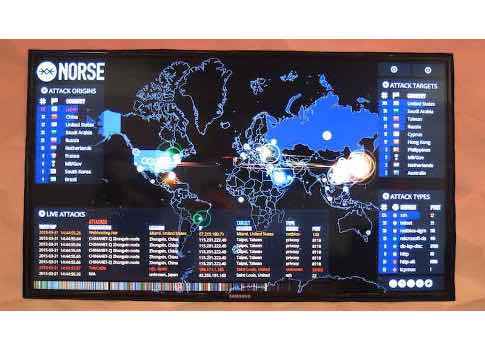
As cyber security is still a new and constantly evolving threat, companies need to set baselines and figure out their risk tolerances before they can decide what measures of protection they should take and how. Included in this baseline are geographic regions and trends. For example, the U.S. is the world’s biggest cyber target, but companies in the Middle East are also prone to many cyber attacks given the dynamics of the region.
However, depending on the company or industry, the biggest threat often comes from the inside, from accidents and unaware employees.
– Eric R. Eissler, is editor-in-chief of Oil & Gas Engineering, CFE Media, [email protected]
ONLINE extra
See related cyber security stories below.



