Cyber threats to control systems are high, frequencies of vulnerability assessments are low, and many organizations are lacking a capable cyber incident response team. Are your systems at risk?
In February 2014, Control Engineering surveyed members of their audience who are directly involved in aspects of control system cyber security within their organizations. The 2014 Cyber Security study asked key questions on cyber security practices, including perceived threat levels, system vulnerability, and recent cyber-related incidents.
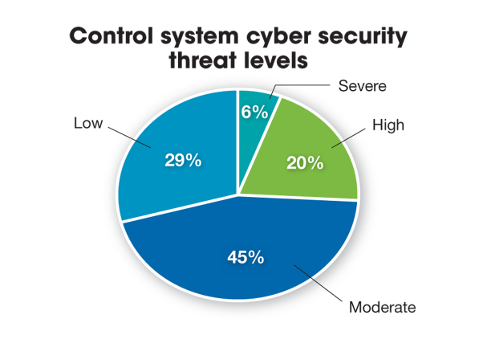
In general, nearly half of respondents perceive the control system threat within their organizations to be at a moderate level, but 1 in 4 cite a “high” or “severe” threat level in their systems.
Malware from a random source with no specific connection to respondents’ respective companies or industries was cited as the most threatening type of cyber-related incident that a control system could experience.
The top three system components respondents are most concerned about are:
- Computer assets that are running commercial operating systems
- Connections to other internal systems
- Network devices.
On the other hand, cyber threats don’t seem to be much of a concern on embedded controllers and connections to the field SCADA network.
Systems vulnerability
When asked about the last time their organization performed any type of vulnerability assessment, one-third of respondents said an evaluation was performed within the past six months, 29% said within the past 12 months, 15% said within the past 18 to 24 months, and an alarming 24% said never.
Of the respondents who indicated that their organization has never performed a vulnerability assessment, 33% have been aware of between 1 and 5 malicious cyber incidents in their control system networks and/or control system cyber assets in the last 24 months. One-third of these incidents were declared as accidental infections, while 20% were targeted in nature, and 47% were a combination of targeted and accidental.
Only 25% of all respondents indicated that their organization’s computer emergency response team appears well trained and capable to detect and respond to cyber-related incidents. Nearly half said either such a team does not exist at their organization, or the existing team is not properly trained to identify and react to these attacks.
Here is where the problem may lie: 71% of organizations are teaching their employees about who to contact in the event of a cyber incident or attack, but not how to properly respond in such a scenario.
Forty-one percent of respondents agreed that having industry-required standards without government involvement would improve or enable their efforts to implement proper control system cyber security controls, while 21% said that no outside involvement would help at all.
– Amanda McLeman is director of research at CFE Media, Control Engineering.


