Cryptology consists of two parts: cryptography, which is the science of encryption algorithms and their use; and cryptanalysis, the science of deriving encryption keys or otherwise decrypting a message by the study of the encrypted message. This industrial wireless technology tutorial explains the basics of cryptology.
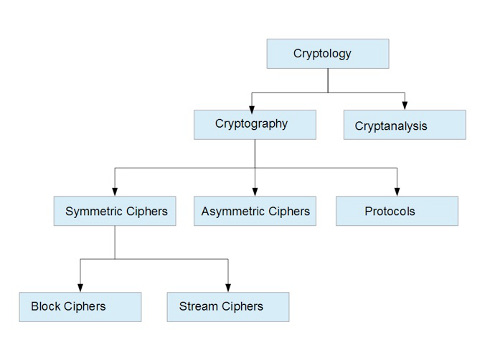
Wireless security uses data encryption, and the study of data encryption is known as cryptology. Cryptology consists of two parts: cryptography, which is the science of encryption algorithms and their use; and cryptanalysis, which is the science of deriving encryption keys or otherwise decrypting a message by the study of the encrypted message. The diagram below shows the general relationship of the branches of cryptology.
Encryption has been with us for millennia. In the last segments, we discussed methods of accomplishing data encryption through the use of protocols, which use various algorithms to transform plaintext data to ciphertext. Earlier in the wireless tutorial series of articles on wireless security, simplified expressions depicting encryption and decryption were explained:
Plaintext —-> Cipher —-> Ciphertext (Encryption)
Ciphertext —-> Cipher —->Plaintext (Decryption)
Wireless cipher for decryption
Common to both processes is the cipher. The cipher is a key or algorithm that allows a transformation of the data. A little history can provide a foundation for an understanding of the technology. When we encrypt data, we transform the data from a readable form that anyone can access to a form that is confidential, "secret" to only the parties that have the key to the encryption cipher, allowing them to decrypt the data.
So what is a cipher? And what exactly is the difference between a cipher, a code, or an encryption algorithm? In essence, they are all the same thing. A cipher is defined as an algorithm used for encryption and decryption. A code is a method of disguising or obscuring plaintext. An encryption algorithm incorporates a cipher and is a method transforming plaintext into a representative symbols, a code. Ciphers and codes take many forms and range from simple and relatively insecure, to extremely complex and virtually impossible to crack.
Every cipher, code, or algorithm has a unique key that allows the parties to the message to encrypt and decrypt the message. The key can be a password, or passphrase, which in turn is converted or mapped to a key. Keys are either "pre-shared," meaning that each party is in prior possession of the key or credentials needed for the exchange, or the keys can be dynamically generated, as explained in the discussion of 802.1X/EAP. The use of pre-shared keys requires a distribution of keys, which in itself raises issues of security.
A cipher is not a protocol, which is a collection of methods, or software, or algorithms that use the cipher as a part of the encryption or decryption process, and is an algorithm in its own right. Two types of ciphers are in common use: streaming and block ciphers. In the former method, data is processed in a serial stream, bit by bit; a bit from the keystream is added to a bit from the plaintext message. Block ciphers encrypt blocks of plaintext bits with the same key; all bits are encrypted simultaneously. A familiar stream cipher is RC4, which like most is small and fast and lends itself to use in systems with limited computing power. The Rijndael Cipher is a block cipher specified by the advanced encryption standard. In the aggregate, modern block ciphers are very software and hardware efficient.
Streaming and block ciphers
Symmetric encryption uses both streaming and block ciphers. A symmetric cryptosystem, sometimes referred to as conventional, shared-key, or single key encryption, was the only kind of encryption used before 1976, when asymmetric, or public-key encryption was developed. Symmetric encryption requires that each party to the transaction know the secret or shared key, which is used for both encryption and decryption. The integrity of the system relies on both parties keeping the key confidential. An example of shared-key encryption would be the user name and password exchange when logging into a wireless router on a small office/home office (SOHO) network.
One problem with symmetric encryption was key exchange; the communicating parties must possess the same secret key and keep it a secret. The issue is then how to securely share the key. The key can be shared directly, but what if the parties are separated by thousands of miles and do not know one another? The transaction begins in a completely untrusted state. A method was needed to allow two disconnected parties to jointly develop a secret key over an insecure channel.
In 1976, Messrs. Diffie, Hellman, and Merkle developed a method of secure key exchange. A pair of keys replaces one secret key, one of which is public and the other is known only to the one party, usually the person who generated the public/secret key pair. This type of encryption is called asymmetric or public key encryption; only one person knows the secret key. The public key is used for encryption, while the secret key is used for decryption. The method of key exchange is known as the "Diffie-Hellman" key exchange.
Assume two parties, Alice and Bob (the classic cryptography couple), want to exchange secret data. Bob generates a random, mathematically related public/secret key pair and makes the public key available to Alice, along with the rest of the world. Alice encrypts the data using the public key and sends the encrypted data back to Bob. Bob uses his secret key to decrypt the data. Alice only has possession of the key used to "lock" the data; Bob has the key that "opens" the lock. Anyone can encrypt the data, but only Bob can decrypt it; as long as Bob keeps the secret key a secret, transmitted data can be assumed secure.
A full discussion of asymmetric encryption and the dynamics of the key exchange are beyond the scope of this wireless tutorial blog. An excellent text for those wishing to learn more about this science is "Applied Cryptography" by Bruce Schneier. There are also several online courses dealing with cryptology.
– Daniel E. Capano, owner and president, Diversified Technical Services Inc. of Stamford, Conn., is a certified wireless network administrator (CWNA), [email protected]. Edited by Chris Vavra, production editor, CFE Media, Control Engineering, [email protected].
ONLINE extras
Wireless has other wireless tutorials from Capano on the following topics:
Wireless security: Extensible authentication protocols
Wireless security: Port-based security, EAP, AKM
Wireless security: IEEE 802.11 and CCMP/AES
Upcoming Webcasts has wireless webcasts, some for PDH credit.
Control Engineering has a wireless page.
https://www.controleng.com/networking-security/wireless.html


