A good, solid understanding of effective cyber security is needed to protect information in a world where wireless communications are standard can have long-reaching effects on a personal and professional level. Note the following seven tips for wireless cyber security and link to more details on each.
Wireless has become the communications medium of choice for many people. However, this is meaningless without a good, solid understanding of effective cyber security and knowing how to protect information whether it’s at home or at work. Consider these tips and best practices for developing a robust wireless security system to protect sensitive information.
1. Develop a cyber security plan
Most cyber security networks are compromised by "social engineering," when a person reveals secure information credentials to an unauthorized person by fraud or subterfuge. A well-conceived cyber security policy that includes education, monitoring, regularly changing passwords, and scrupulous maintenance of employee records and security credentials can virtually eliminate the threat posed by social engineering attacks.
2. Don’t assume the network is ever secure
No cyber security program is ever 100% secure. There is always an element of risk, particularly when dealing with an unbounded medium like wireless. It should never be assumed that any wireless communication is secure when using a public Wi-Fi hotspot or a foreign access point. It is not wise to assume that any wireless communication is completely secure or private. It is up to the client to ensure it is using the latest and strongest security methods. Being aware and vigilant is the best option.
3. Pick a strong password
A strong password for cyber security networks—and anything else used on the Internet, for that matter—makes it harder for hackers to use brute-force techniques to compromise the user’s network and private information. Basic guidelines include a minimum of 10 characters. Adding capital letters and numbers are highly recommended. While the password should be complex, it should also be something the user can type accurately and remember with little difficulty. And while it goes without saying: The password should never be divulged to anyone; if the password is shared the system is immediately compromised.
4. Don’t go for the bare minimum
Obsolete cyber security methods such as MAC filtering and service set identifier (SSID) cloaking are still used, but they provide minimal, if any, security on a wireless network. MAC filtering denies or allows a user access based on his unique hardware (MAC addresses). However, it is easy for hackers to spoof, or clone, an authorized device’s MAC address. SSID cloaking or hiding is also ineffective because it does not secure the network or any data, and it’s easy for hackers to compromise the system if mobile devices are involved.
5. Encrypt the data
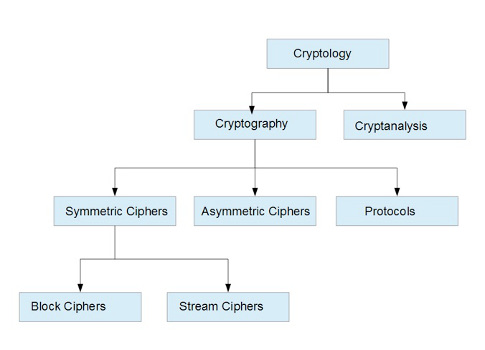
Encryption is designed to protect and obscure sensitive data so an outsider cannot read it. There are several methods of encryption, but in every case a cipher is used. The cipher protects the algorithm used by the encryption protocol. An intruder can intercept data broadcasts over a wireless network, but encrypting that data makes it very difficult for someone to decipher the information unless he or she has the proper decryption key.
6. Stay up to date with the latest protocols
Wireless cyber security networks are constantly tested for vulnerabilities. It is a fact that eventually the latest and greatest security methods will be compromised. Wired equivalent privacy (WEP) was tested and cracked; temporal key integrity protocol (TKIP), which was designed as an interim measure, was also cracked. Wi-Fi protected access II—pre-shared key (WPA2-PSK), the current wireless network system, will also be beaten and replaced by something else. It is inevitable. It is the responsibility of system administrators to implement a solid security policy that supports and enhances physical- or software-based security solutions.
7. Be vigilant and aware
Diligence in monitoring and intrusion detection is essential to maintaining a secure system. Upgrading system software and equipment will allow a degree of "future-proofing" and pre-emptive defenses against sophisticated attacks.
To err is human, but following these tips provides some guidance in a world continuously changing and evolving at speeds most could not even comprehend at the turn of the century.
– Daniel E. Capano, owner and president, Diversified Technical Services Inc. of Stamford, Conn., is a certified wireless network administrator (CWNA). He can be reached at [email protected]. Edited by Chris Vavra, production editor, CFE Media, Control Engineering, [email protected].
Key concepts
- Best practices can improve wireless cyber security.
- Develop a wireless security plan that works best for you.
- Don’t assume strong passwords and encryption protocols make your network safe.
Consider this
Do you have a plan specific to wireless cyber security in addition to wired security?
ONLINE extra
These wireless tutorial blogs from Capano provide more information on each topic.
Wireless security tutorial: Wireless intrusion detection systems and wireless attacks
Wireless security tutorial: Cryptology basics, fundamentals
Wireless security legacy, background
Wireless security legacy