Four key steps to help your organization achieve IT-OT convergence
IT and OT teams often seem like they're in different worlds. To bring true IT security into the OT environment, here are four key steps to help organizations create IT-OT convergence.
In many industrial organizations, information technology (IT) and operational technology (OT) teams are from different planets. They have separate objectives, priorities, skills, metrics and even language. IT-OT convergence, or better said “connected industries,” requires these groups to work together to achieve the key business objectives of greater efficiency and output, as well as enhanced security of these newly connected systems.
Through IT-OT convergence, systems that were formerly “air-gapped” or “islanded” from enterprise IT and its access to the internet and communication applications, such as email and cloud interfaces, can utilize this enterprise infrastructure to take advantage of the scale and power of big data analytics. But with this added benefit comes the risks present in IT networks: ransomware, hacking for espionage and, even worse, potential disruption of physical processes to cause physical damage.
Chief information security officers (CISO) and chief information officers (CIO) are now being asked by their boards of directors to secure these systems and ensure they have the same level of security as the other devices within the enterprise. As a result, IT leaders are looking to increase the integration of IT and OT in driving standardized cybersecurity across all endpoints and networks in the enterprise.
Unfortunately, operating technology (OT/ICS) assets like human machine interfaces (HMI), servers, programmable logic controllers (PLC), relays, real-time automation controllers (RTAC) and other intelligent electronic devices are excluded from the cybersecurity processes in most organizations for a variety of reasons. These can include everything from organizational boundaries and regulatory requirements, to IT personnel’s lack of skills with OT systems. Further, OT/ICS teams are consistently under headcount pressures as operations look to increase efficiency.
Consequently, many of the foundational elements of cybersecurity are not present in OT/ICS. Inventories are not accurate, configuration and patch databases are out of date, and account and user access management are not well managed. In part, this is because the tools required to automate these processes have not been available given the sensitive, unique and embedded nature of the assets in OT/ICS.
Courtesy: Verve Industrial Protection
To bring true IT security into the OT environment and achieve robust, consistent security management, here are four key steps for organizations to help IT and OT work together:
1. Create shared education and awareness of IT-OT convergence.
The fundamental gap in IT and OT begins with a lack of understanding of the objectives and goals of each function. For example, IT teams regularly try scanning OT systems with traditional IT vulnerability scanners and “bricking” OT devices on a consistent basis, without realizing the problems they’re causing. Similarly, OT teams will often say, “We can’t patch,” as a blanket statement without understanding IT’s security goals or the practical ways of potentially patching certain assets at specific times.
The first step organizations can take toward successful IT-OT convergence is a commitment to joint education and awareness sessions. Often, this can occur over a series of four or five joint workshops where key OT leaders share the details of their business processes and objectives, and IT teams share their security goals and typical approaches. These workshops will allow both departments to discover how to communicate with each other and gain an understanding of their objectives and limitations.
2. Design an IT-OT security organization that addresses the needs of both sides.
There is no perfect enterprise model. However, organizations have found success creating a combined security leadership team, with OT leaders joining their IT counterparts in senior leadership positions. Others have adopted IT security leadership but included significant input from OT into the tools, processes and standards applicable to their systems.
Some of the biggest mistakes enterprises make are having a token OT representative on the security leadership team or recruiting one or two midlevel OT-experienced personnel to the team as representatives of OT. In almost every case, this ends with the OT representatives being subsumed into the IT organization and having limited impact. The most successful companies assign a key, senior and truly respected OT leader, and give them true authority within the overall security organization.
3. Establish an OT systems management program.
OT systems management (OTSM) is the key to a robust OT security program. It involves the following elements:
- Asset inventory management
- Lifecycle management, including defining system requirements to achieve desired physical system outcomes, establishing specifications to ensure reliability and security, supply chain management and control over these systems, and replacement of outdated components
- Configuration management
- Patch and vulnerability management
- Network and system design
- User and account management
- Log and performance monitoring for reliability and security
- Incident and trouble response
- Backup and restore.
IT often takes these fundamental components for granted because they’ve been a core part of IT systems management (ITSM) for years. But in OT, most of these tasks are not completed on a consistent basis. As a result, OT lacks the foundation that IT security is built on. Organizations often want to jump to threat detection or micro-segmentation before understanding the assets on the network, the users on the systems, etc.
By establishing a foundation of OTSM, IT and OT teams can start to work together effectively from a similar basis of asset management.
A robust OTSM program leads to a number of other key benefits, including:
- Clarity of all hardware and software in the network to ensure vulnerabilities are identified quickly
- Properly updated and configured systems, reducing the surface area for attacks
- Operationally efficient updating of systems to provide automation on key operational tasks
- Consistent reporting and monitoring across IT and OT for simplified reporting of progress
- More effective and advanced security controls since they’re built with proper visibility and access to the underlying endpoints and network information.
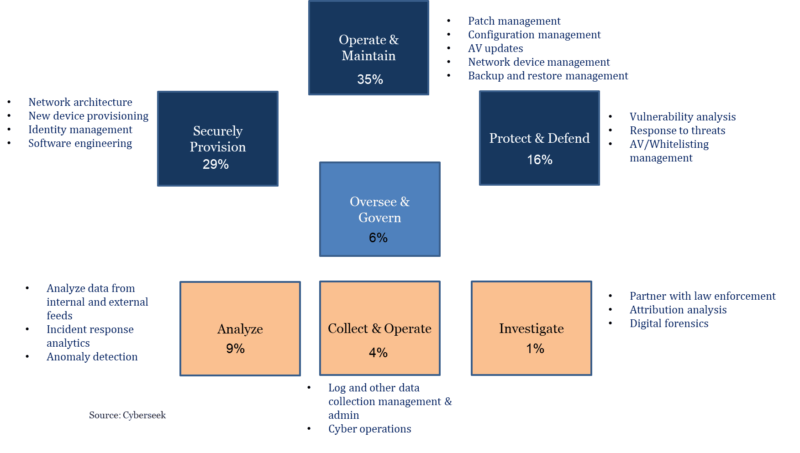
4. Skill development
To really achieve IT-OT convergence, an enterprise needs to build the key security management skill sets in OT. In IT, almost all systems management tasks can be completed centrally. However, in OT, the unique and sensitive processes may require local OT knowledge before security functions such as patches or configuration management are undertaken. Therefore, workforce development around key OTSM concepts — such as patching, configuration management, password management, etc. — on traditional OS devices and networking equipment, as well as the range of embedded operational devices, will be necessary. One can certainly applaud the significant training available around cybersecurity analysis, investigation, threat hunting, etc., but an equal amount of focus needs to be placed on the other 70% of cybersecurity, including the foundational elements of systems management.
Organizations need to adhere to these four key steps of building awareness, designing the right organization, establishing OTSM and developing the right skills in order to get IT and OT teams to effectively work together and drive true security capabilities in both departments.
– Verve Industrial is a CFE Media content partner. And check out John Livingston talking about increasing industrial cybersecurity threat and the cyberattacks on SolarWinds and Oldsmar in the Industrial Cybersecurity Pulse Expert Interview Series.
Original content can be found at www.industrialcybersecuritypulse.com.
Do you have experience and expertise with the topics mentioned in this content? You should consider contributing to our CFE Media editorial team and getting the recognition you and your company deserve. Click here to start this process.