Manufacturers are continuing to be a major target for cybersecurity attacks and need to plan and design for the future. Four steps on how to do this are highlighted.

OT cybersecurity insights
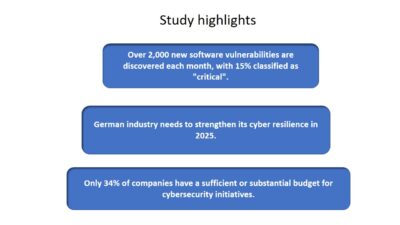
- Manufacturing faces escalating cyber threats due to outdated systems and lucrative targets. Companies must prioritize proactive cybersecurity measures to mitigate risks effectively.
- Strategies like zero trust security, adherence to standards, and a defense-in-depth approach are critical for manufacturing’s resilience against evolving cyber threats.
Manufacturing is the most-targeted industry in cybercrime, representing a fifth of all cyber extortion campaigns. That percentage will only increase. Bad actors, whether they’re represented by nation-states, criminal organizations or on their own, recognize manufacturers have a lot of money and are particularly vulnerable. Many facilities were built and designed before the internet and so were their systems.
“Most of us are not prepared for the attacks,” said David Bader, VP of business development, Eurotech, in his presentation “Designing for tomorrow’s cybersecurity challenges” at Automate 2024 in Chicago.
A lack of training is another challenge and companies are often having to play catch-up with their own education as well as their colleagues. It creates a porous and inefficient system that’s more like a game of Whac-a-Mole.
Companies and governments and standards realize what’s happening out there and are taking steps to be more proactive, which Bader said is critical. No one, he said, can afford to bury their head in the sand. They have to act. For companies, he said the reason is simple. A successful cybersecurity attack has a significant impact on the bottom line.

While no company will be perfect in their approach, Bader said they can get on the right foot with these four steps:
-
Secure by design
-
Zero trust security
-
Adhere to current cybersecurity standards
-
Follow a defense-in-depth approach.
Build a secure cybersecurity platform
Even if the company has a lot of legacy equipment to contend with, Bader said companies can build a strong foundation for the future with a six-step approach:
-
Design for security from the start
-
Start with a cybersecurity risk assessment
-
Build security features into products and solutions
-
Implement security throughout a product’s lifecycle
-
Use secure configurations by default
-
Leverage certifications to ensure a solid security baseline.
The six steps feed into one another and requires transparency from all sides and strong communication. It also requires companies to be vigilant and wary of what is happening around them.
Zero trust security
Zero trust operates on the principle that no one can be trusted and the systems that are used to create and maintain the platform.
“We know everything is valid from the supply chain to the provisioning and operational level,” Bader said.
With a strong protocol in place, companies can create a system to successfully commission, provision and connect devices securely through the framework that have already been established and make things more efficient.
Adhere to the standards
Bader said companies should follow and adhere to standards such as ISA/IEC 62443 and ensure a solid approach to device identities. When they’re choosing products, they should be secure by design and are certified for IEC 62443-4-2 for industrial applications. This helps ensure a globally-recognized framework that enhances security, reduces validation efforts and contributes to critical infrastructure stability.
The problem, Bader said, is many companies are not as certified as they should be and they need to be more serious in their approach.
-
An increasing number of intentional attacks are targeting industrial automation and control systems. Bader said companies should prioritize many things including:
-
Distinguish between individual human or non-human users interacting with the component, which increases the ability to trace the source for user activity that may constitute an attack.
-
Provide the ability to tailor human role definitions to reflect site operations and reduce unnecessary insider access.
-
Close inactive communication sessions that remain open as potential attack vectors.
-
Verify communication sources to the component.
-
Increase assurance that code in execution comes from a trusted sources and has not been subjected to tampering.
Developing a defense-in-depth strategy
A defense-in-depth strategy is to provide redundancy in the event a security control fails or a vulnerability is exploited. Bader highlighted several things companies can do to mount an effective strategy such as:
-
Implement multiple layers of defense using security controls
-
Conduct a cybersecurity risk assessment and implement network segmentation
-
Provision modern industrial Internet of Things (IIoT) devices and systems with unique identities and credentials
-
Prioritize and implement operational technology (OT) and IIoT-specific patch management and define appropriate update mechanisms.
-
Secure data manufacturing at the edge and the cloud.
Connectivity will only be increasing going forward and companies that don’t have a solid, consistent plan are putting themselves in danger of being hacked. Crime does pay in this instance and the ransom alone isn’t the only cost: If operations are disrupted, the cost will be far more than whatever the original price was.
Chris Vavra, senior editor, Control Engineering, WTWH Media LLC.