It is important to understand the interaction between safety and security in process control applications to make better overall decisions.
Every production process comes with inherent risks. To achieve the greatest degree of safety and security, it is vital to implement an effective separation of the process control and safety systems, which is required for functional safety and cybersecurity standards. There is a lot at stake, including the employees’ health, the company’s assets, and the environment.
For a better understanding of the interaction between safety and security, it is helpful to clarify several terms. There are numerous definitions of safety. A general definition of safety is the absence of danger. This means a condition is safe when there are no prevailing hazards. It often is not possible to eliminate all potential risks; especially in complex systems.
A more common definition of safety is the absence of unacceptable risks. Reducing risks to an acceptable level is functional safety’s task. An application’s safety depends on the function of a corresponding technical system, such as a safety controller. If this system fulfills its protective function, the application is regarded as functionally safe.
This can be clarified with these two examples: oil flowing out of a pipeline and endangering people in the vicinity is a safety issue. A system that cannot prevent icing in a pipeline, even though that is supposed to be its task, and then a critical situation arises, is a functional safety issue. Functional safety systems protect people, facilities, and the environment and are intended to prevent accidents and avoid downtime of equipment or systems.
Separate layers reduce risks
The process industry increasingly is becoming aware of the importance of relevant standards for the safety and profitability of systems. Technical standard IEC 61511, Functional safety – Safety instrumented systems for the process industry sector, defines the best way to reduce the risk of incidents and downtime. It prescribes separate safety layers for control and monitoring, prevention and containment, as well as emergency measures (see Figure 1). Each of these three layers provides specific functions for risk reduction, and collectively they mitigate the hazards arising from the entire production process.
IEC 61511 also prescribes independence, diversity, and physical separation for each protection level. To fulfill these requirements, the functions of the different layers need to be sufficiently independent of each other. It is not sufficient to use different I/O modules for the different layers because automation systems also are dependent on functions in I/O bus systems, CPUs and software. To be regarded as autonomous protection layers in accordance with IEC 61511, safety systems and process control systems must be based on different platforms, development foundations, and philosophies. In concrete terms, this means the system architecture must, fundamentally, be designed so no component in the process control system level or the safety level can be used simultaneously.
Rising risk
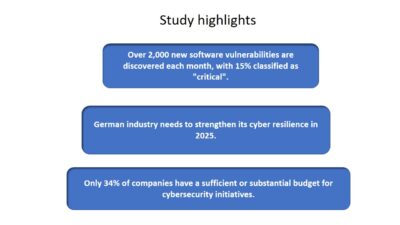
In the last 10 years, the risk of cyber attacks on industrial systems has risen due to increasing digitalization. In addition to endangering information security, these attacks increasingly pose a direct threat to system safety. System operators need to be aware of these risks and address them. This can be achieved in a variety of ways. Unlike functional safety systems, which are intended to protect people, these systems and measures protect technical information systems against intentional or unintentional manipulation as well as against attacks intended to disrupt production processes or steal industrial secrets.
Safety and security have become more closely meshed. Cybersecurity plays a key role, particularly for safety-oriented systems, because it forms the last line of defense against a potential catastrophe.
Standards define the framework
Compliance with international standards is necessary in the design, operation, and specification of safety controllers. IEC 61508, Functional Safety, is the basic standard for safety systems, which applies to all safety-oriented systems (electrical, electronic, and programmable electronic devices). IEC 61511 is the fundamental standard for the process industry and defines the applicable criteria for the selection of safety function components.
The IEC 62443 cybersecurity series of standards for information technology (IT) security in networks and systems must also be considered. It specifies a management system for IT security, separate protection layers with mutually independent operating and protection facilities, and measures to ensure IT security over the full life cycle of a system. It also requires separate zones for the enterprise network, control room, safety instrumented system (SIS), and basic process control system (BPCS), each of which must be protected by a firewall to prevent unauthorized access (see Figure 2).
Cybersecurity by design
Safety and security are closely related aspects of process systems, which must be considered separately and as a whole.
Standardized hardware and software in process control systems require regular updates to remedy weaknesses in the software and the operating system. However, the complexity of the software architecture makes it difficult or impossible to assess the risks analytically, which could arise from a system update. For example, updates to the process control system could affect the functions of the safety system integrated into the control system.
To avoid critical errors with unforeseeable consequences in safety-relevant processes as a result of control system updates, the process control system must be technologically separate from the safety system. For effective cybersecurity, it is not sufficient to upgrade an existing product by retrofitting additional software functionality. Every solution for functional safety must be conceived and developed with cybersecurity in mind, right from the start. This applies equally to the firmware and the application software.
Effective protection
An example of effective protection is a proprietary operating system specifically designed for safety-oriented applications and runs on autonomous safety controllers. It includes all functions of a safety PLC and excludes all other functions, making it immune to typical attacks on IT systems. The CPU and the communication processor need to be separate for operational security even in the event of an attack on the communication processor. The controllers allow several physically separate networks to be operated on a single communication processor or processor module. This prevents direct access to an automation network from a connected development workstation. In addition, unused interfaces can be disabled individually.
A common feature of the process industry standard and the cybersecurity standard is the required separation of the SIS and the BPCS. This independence of safety systems is a good idea from a practical and economic perspective. The SIS and BPCS have, for example, very different life cycles and rates of change. System operators are free to choose "best-of-breed" solutions from different manufacturers.
Systems independent of the process technology, which can be integrated into process control systems despite physical separation, offer the highest degree of safety and security for critical applications. They are the best way to increase the operational reliability and availability of process systems and improve the overall profitability of a production process.
Dr. Alexander Horch is head of the R&D and product management business area at HIMA Paul Hildebrandt. This originally appeared in a September 10 article on the Control Engineering Europe website. Edited by Chris Vavra, production editor, Control Engineering, CFE Media, [email protected].
MORE ANSWERS
www.controleng.com keywords: process control, process safety
- Functional safety systems protect people, facilities, and the environment and are intended to prevent accidents and avoid downtime of equipment or systems.
- The risk of cyber attacks on process control system has increased due to increased digitalization and can pose a major threat to system and worker safety.
- Systems independent of process control technology offer the highest degree of safety and security for critical applications.
Consider this
What other steps can companies take to better protect their process control systems from safety and security risks?