Traditional distributed control system (DCS) and supervisory control and data acquisition (SCADA) systems designs can be improved with industrial digital transformation. Seek industrial interoperability, modularity, conformity to standards, including security standards, scalability and portability.

Don’t let early success with operational technology (OT) connectivity stall technology innovations now for Industrial Internet of Things (IIoT) and industrial digital transformation (DX). Advanced process control system designs incorporate interoperability, modularity, standards, scalability and portability. A decade or so ago, when promoters of the IIoT and DX started gaining attention, a frequently emphasized point was how everything from the device level on up could and should be interconnected. Experienced engineers and technicians responsible for designing and maintaining legacy industrial automation systems in process manufacturing facilities could roll their collective eyes and say, “We’ve been doing that forever. Our control systems are all about connectivity and integration. What’s the big deal?”
While such people can claim some legitimate bragging rights about those early systems, much of the industrial automation technology soon got bogged down, allowing the IT world to pass it by. The role of networking and interconnectivity in the context of OT and process control has been complex and continues to evolve, but by borrowing from IT. To understand where OT is headed, consider how we arrived where we are today.
Dawn of automated process control, DCS, SCADA
Starting 40-plus years ago, with the world’s first distributed control system (DCS), process automation systems have consisted of self-contained control and visualization components. Supervisory control and data acquisition (SCADA) systems were often used for outside-the-fence assets such as pipeline systems and wellheads.
Both architectures collect data from process instruments and respond by sending actions to actuators, and both can control multiple loops simultaneously to handle complex processes. As programmable logic controllers (PLCs) gained sophistication, they also began to serve as small-scale controllers.
Early on, these types of systems were built using proprietary hardware and software, operating in isolation without connections to other networks. Operators had to reside in a centralized control room or command center because human-machine interfaces (HMIs) did not support remote access. Any information provided to personnel other than operators was delivered via reports, which often had a significant time lag.
Commercial technologies help industrial operations
Over time, proprietary hardware and software gave way to commercial off-the-shelf (COTS) equipment, primarily PCs, providing new mechanisms for industrial connectivity. With that connectivity, process automation systems could interface with corporate networks at the facility, extending eventually to the Internet. Data access and even actual control from any location became possible. Over time, one isolated DCS or SCADA system (Figure 1 left) eventually found itself part of a much larger real-time network (Figure 1 right), which could eventually connect to anything.
This broad history lesson helps provide a contextual framework for considering what comes next.
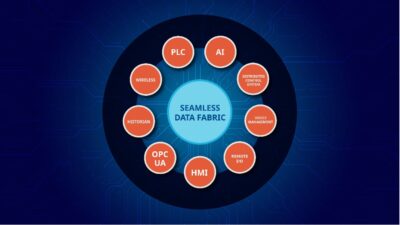
Forward-looking companies concerned about implementing industrial DX strategies must consider how their DCS and SCADA platforms fit into the larger picture. What will these systems look like to perform their traditional functions in a more complex environment where the layers of the automation pyramid are blurring (Figure 2) and losing distinctiveness?
IT, OT, virtualization, cloud for IIoT
With IT and OT convergence combined with virtualization technologies, many engineering and software applications are moving to the cloud. Integrating cloud technologies allows process control systems to perform edge computing and serve as data sources for the IIoT.
Cloud-based environments can integrate data from multiple sources and improve data availability to support analytics and decision making.
Modernizing industrial control systems with open architectures
Taking advantage of cloud-based environments, IIoT, and edge computing requires process manufacturers to modernize aging DCS and SCADA platforms. One of the side benefits of the drive toward DX is moving to a more open and secure system architecture and design.
Two standards, NAMUR Open Architecture (NOA) and Open Process Automation Forum (OPAF), are driving open architecture initiatives (Figure 3) in industrial automation by moving away from proprietary architectures. Both describe how vendor-neutral systems can use state-of-the-art equipment and functions, avoiding the common problem of vendor lock-in. Key concepts of OPAF include:
- Interoperability
- Modularity
- Conformity to standards
- Compliance with security standards
- Scalability
- Portability.
Within NOA, an independent domain called monitoring and optimization (M+O) is prepared separately from the existing system. It collects data directly from robots and drones as well as new sensors for corrosion, sound, vibration and other maintenance-related variables. Data in the existing system is imported via OPC UA so advanced control, analytics and diagnostics can be realized in the field.
Security for industrial controls, automation
To provide security, compatibility with zone design (as recommended by ISA/IEC 62443 Security for industrial automation and control systems) is enhanced so system design and maintenance can be performed easily. The standard provides a framework to address and mitigate security vulnerabilities in process control systems. See more on industrial cybersecurity below.
The main problem users often encounter when trying to implement these concepts is incompatibility with older control system platforms. Legacy installations not upgraded incrementally over the years may be unable to support new capabilities. Discussions with the original vendor may be difficult if the recommended solution is a rip-and-replace full system upgrade. These are expensive due to the purchase and integration price, plus lost production time during the installation combined with a slow restart.
The bright side is it should not be necessary to ever undertake such a mass replacement again since today’s control systems are open and interoperable, so any part can be upgraded when necessary, with minimal or no disruption to the whole.
Baking in industrial cybersecurity
Many existing DCS and SCADA systems lack provisions for cybersecurity. Since they were conceived originally as existing in isolation, there was no path to attack from the outside. The need for protection was not considered. Once companies began connecting these systems to external networks, it was clear they represented a soft target. The only practical approach was hardening the perimeter. There are some methods to improve internal security, but the effectiveness of “bolt-on” approaches varies.
DX has created a need for secure networks since it depends on openness. Fortunately, the need for security is matched with improved methods as IT and OT converge. For example, with SCADA systems, the traditional architecture connects field devices to remote terminal units (RTUs) for data consolidation and translation. This makes RTUs a primary target for attackers due to their strategic position and vulnerability. New DX technologies are phasing out RTUs in favor of edge devices, which are easier to defend.
IT and OT convergence does not mean networks are mixed randomly, as convergence implementation teams must instead make careful evaluations regarding the segregation of OT networks from corporate networks and the Internet. Privilege access must be controlled at site and process levels, along with cross-site communications.
Any major DX undertaking should begin with a vulnerability assessment to determine any areas requiring particular attention. ISA/IEC 62443, along with the National Institute of Standards (NIST) 800-160 Volumes 1 and 2, Developing cyber resilient systems: A systems security engineering approach, offers resources and guidelines for network administrators and cybersecurity experts. As third-party consultants and integrators are being considered, their cybersecurity portfolio (Figure 4) should be carefully analyzed to ensure sufficient coverage and depth for a large-scale undertaking.
Competence in IT and OT domains is critical to handle cybersecurity implementations.
DX, future of process control, self-learning designs
DCS and SCADA systems, driven by DX developments, are changing and evolving and the journey is only starting. This presents challenges to process manufacturers, especially when considering a difficult decision to launch a major system upgrade. No manufacturer should be satisfied with the idea of the same capabilities running on newer hardware.
Any new system will be more modular, allowing sections to be upgraded or replaced as necessary when new capabilities are added. This is only a start. Industrial automation will add capabilities that can only be imagined now.
For example, a DCS will have self-learning abilities to better understand the processes under its control. It will develop the ability to execute complex control functions such as procedures (start-up, grade change, etc.) automatically with minimal, or even no, operator intervention. Plants will reduce accidents and downtime resulting from human errors while achieving optimal operation.
Greater system connectivity will be able to support integrated operations centers, along with dynamic operator guidance facilitated by high-quality alarm systems. These developments will help manufacturers achieve new, higher levels of system optimization and safety. Dynamic digital twin simulators allows operators and managers to evaluate changes to operating conditions by predicting process behaviors in advance.
These capabilities will use open systems to support IIoT and cloud-based operations—including OPC UA and message queuing telemetry transport (MQTT)—along with other IT connectivity protocols, such as simple network management protocol (SNMP) and internet control message protocol (ICMP).
Getting help for an industrial DX project
Few process manufacturers have the internal resources to effectively design and manage all of these changes. Fortunately, there are companies, integrators and consultants able to provide guidance throughout a DX project. Any service provider under consideration must draw upon proven control technology across a range of automation architectures, efficient control strategies, and advanced solutions. These are major undertakings with their own risks, but the rewards, when implemented effectively, are enormous.
Kevin Finnan is a digital transformation and industry marketing consultant at Yokogawa Corporation of America. Wataru Nakagawa is a system product content marketing manager for Yokogawa Electric Corp. Edited by Mark T. Hoske, content manager, Control Engineering, CFE Media and Technology, [email protected].
MORE ANSWERS
KEYWORDS: Process control system, industrial digital transformation
Commercial technologies help industrial operations
IT, OT, virtualization, cloud for IIoT
Modernizing industrial control systems with open architectures
CONSIDER THIS
Are you overlooking industrial digital transformation innovations because “we’ve already done that”?
ONLINE extra
Learn more about the roles of DCS and SCADA in industrial digital transformation from Yokogawa.